Meltdown and Spectre were a hot topic this week for anyone who uses a computer. That would be a huge number of affected systems mainly because Intel chips were highlighted as having a design flaw (apparently for many years) that presents a “potential” Security weakness that could be capitalized on for some malicious activity. ARM and AMD chips also are identified as having the same or similar problems. The issue is how the CPU passes control to the kernel operations, then takes control back. Speculative execution is used to increase performance, but due to the CPU vulnerabilities, sensitive data may be exposed. Meltdown affects the isolation between applications and the operating system. This requires hardening the system against any exploits that could leverage these vulnerabilities. Anyways, it would be a good idea to update your operating systems security patches and antivirus.
Now as everyone scrambled to patch their operating systems (Windows, Mac, and Linux) the concern now is a possible performance hit due to the fix. Of course, how can you be certain that your system is affected by the vulnerability or the performance hit from the patching especially if you never check to see how your CPU/CPUs are currently performing.
WINDOWS
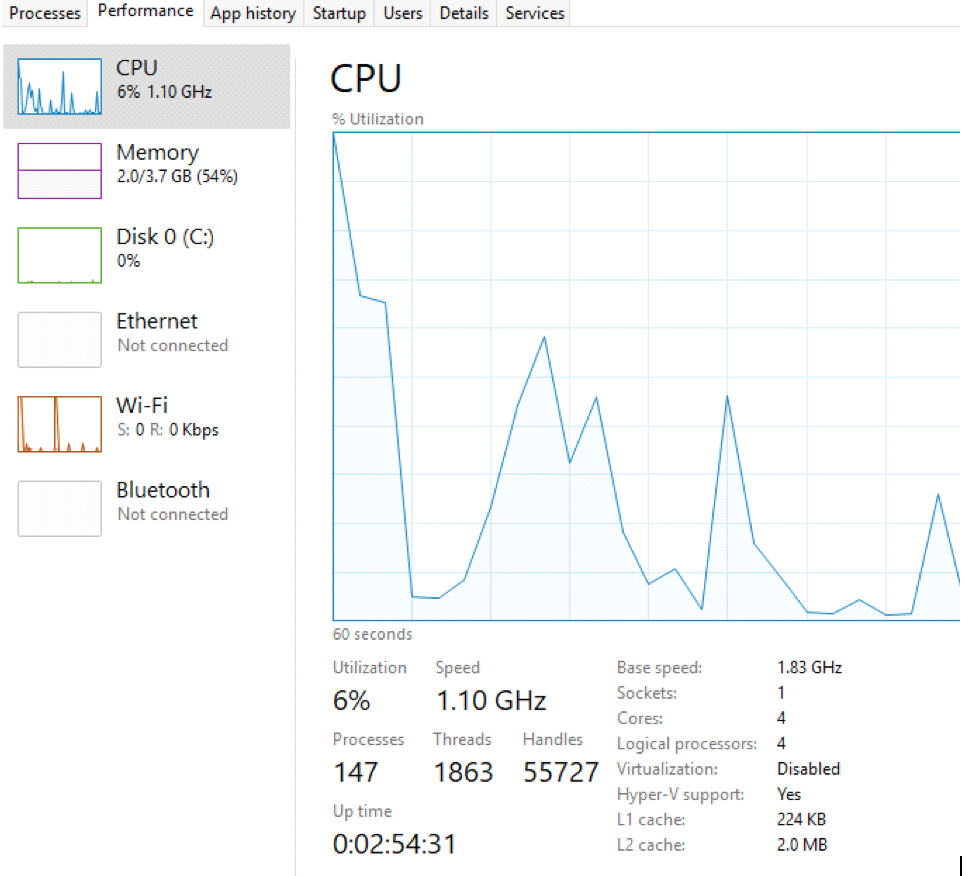
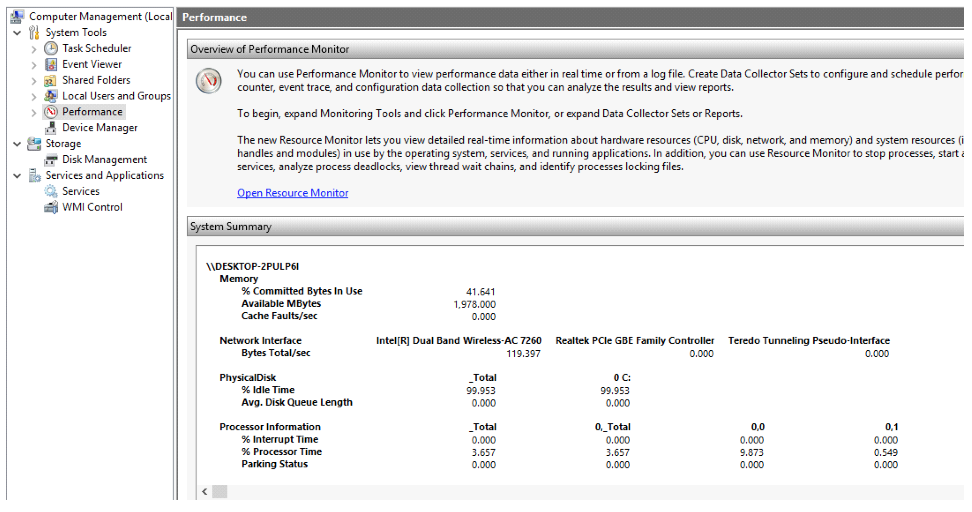
In Windows 10 it’s pretty easy to open up Task Manager and select the Performance tab to see your CPU Base Speed, Utilization, and Speed. It’s quick and handy. You can play with the graph a little to see a summary view, Logical Processors. What you might want to check is if your system currently has the flaw issue.
If your familiar with Powershell you can do s little testing.
When you run Powershell as Administrator you would run a few commands:
Install-Module SpeculationControl
You may then need to run:
Set-ExecutionPolicy Bypass
If that runs through ok, then the actual check is done by running:
Get-SpeculationControlSettings
When you’re all done looking through the results don’t forget to set the execution policy back to “Restricted” by running:
Set-ExecutionPolicy Restricted
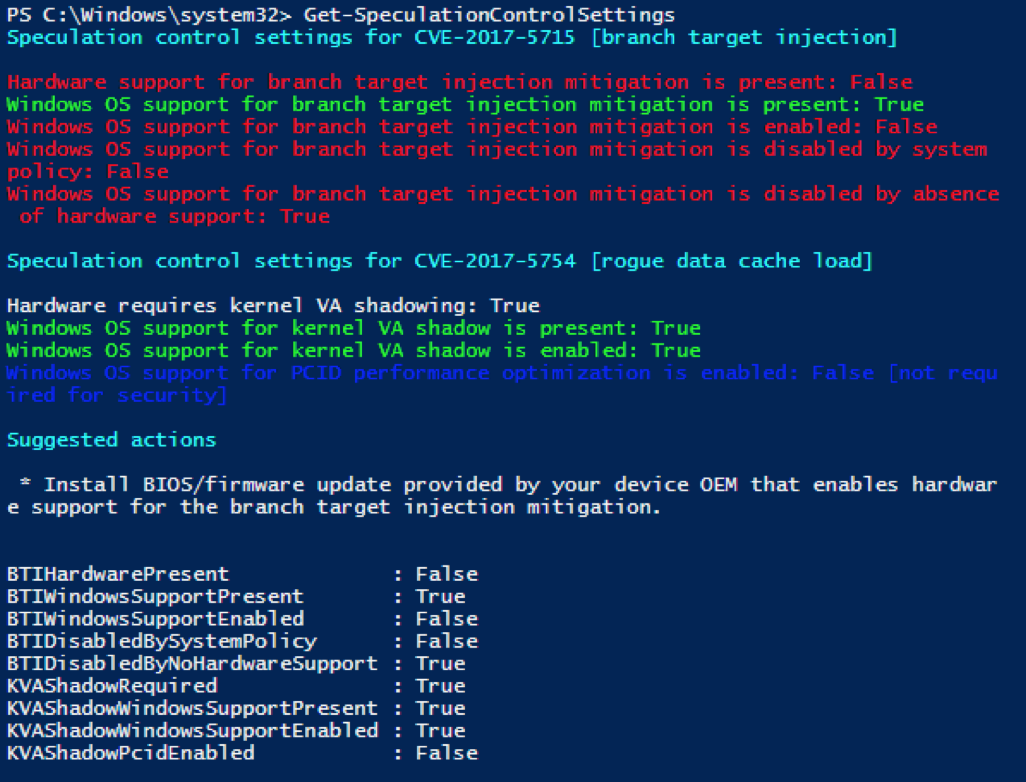
Run on my old test machine ThinkPad (After checking my updates for KB4056892 OS Build 16299.192)
LINUX CPU check:
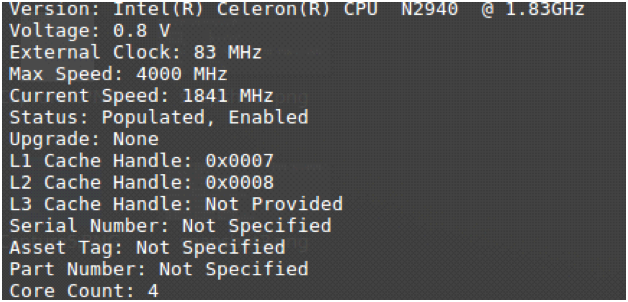
In Linux it’s also very easy to check on your CPU.
Here are a few quick command line checks you can do with SUDO:
# dmidecode -t 4
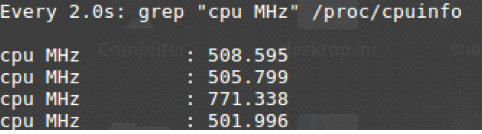
# watch grep \”cpu MHz\” /proc/cpuinfo
A lot more detail can be had with:
# less /proc/cpuinfo
To check your Linux system
cat /proc/cpuinfo
This will contain a line that states:
bugs :cpu_insecure
if your kernel has KPTI patch
As usual, I would suggest keeping your distro’s security up to date with apt update and apt upgrade.
Will newer chips be the best solution – probably? I’m very interested in the AMD chips now, mostly because they might be less impacted. That’s still a little fuzzy, but if I do pick up a new pc anytime soon – I’ll take a serious look at the AMD chips. We shall see how all this pans out in the next few weeks – or months. For now, I think I’ll wait. So, keep an eye on the performance of your system and see if you notice any significant impact as new patches get rolled out. Usually, you want to get more performance out of your systems, not less.