The “Microsoft” Ubuntu command line “App”
Sometimes you find yourself working on a Windows-based machine, have to perform a quick task that might normally be very straightforward on a LINUX machine, and you don’t want to spend too much time fumbling through the GUI pointing and clicking until you stumble across what you’re looking for.
My first gut instinct usually is to get to the command line quickly and work from there.
I installed the “Microsoft” Ubuntu command line “App” on a Windows 10 test machine recently hoping it would become the perfect solution to such situations, but it has been a disappointing experience so far. Maybe I’ll have a better opinion after I spend more time with it, but I doubt I’ll see this installed on too many machines I run into – at least for a while. Luckily Windows command line tools are pretty robust – especially PowerShell.
As a side note, I really find Sysinternals very useful as a nice set of tools for some very interesting challenges you might run into while doing some diagnostic investigation on problematic systems.
For the most part, Windows usually has some nice built-in diagnostic tools – if you know where to look and can find them in a timely manner.
I had a question come up recently about port connections. Usually, I suggest Wireshark as a go-to tool for any supporting operating system, but this situation was for a system that did not have it available – disregarding the fact that you might or might not have the ability to monitor the packet traffic with a tap or port forwarding access via a test laptop. The discussion was on using the computer in question for any diagnostics – and of course, it wasn’t a LINUX machine. Anyhow, here’s a few ideas I floated for such situations – try a few if you haven’t already and see what you think.
Finding port connections in Windows
Use Wireshark to parse out port numbers by adding Destination and Source port columns for both TCP and UDP port numbers. Under each corresponding Wireshark header right-click on destination/source and apply as a column. Edit the name to differentiate between UDP or TCP.
Filtering for a specific protocol number is just as straightforward.
Examples:
tcp.dstport == 80
tcp.srcport == 80
![]()
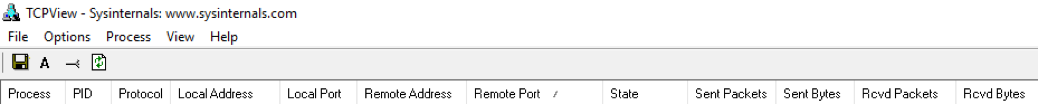
If you’re a fan of Sysinternals you may find TCPView a nice alternative to monitor your PC’s connections – close to a real-time view of connections made and unmade.
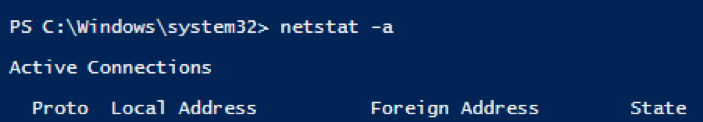
Either from the basic Windows CMD or from within Powershell “netstat” similar to its LINUX long-lost cousin is a simple and quick way to view connection status.
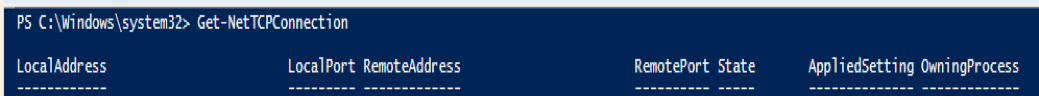
While you’re working in Powershell, check out network connections with Get-NetTCPConnection.
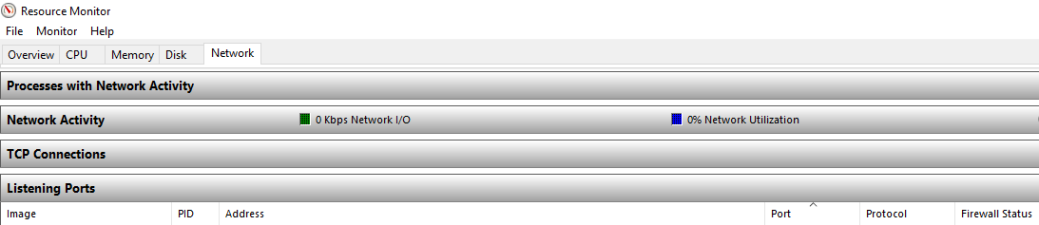
If your set on using the GUI on Windows, the “Resource Monitor” Network – Listening Ports works quite well.
Back on Linux, you can run netstat, lsof, ss, or nmap.
Each has many options and allow you to customize your scans.
Here a few quick checks:
netstat -a | grep CONNECTED
or
lsof -i
or
ss | less
You could always load nmap and scan your own local ports as an alternative port check.